Well here we go again, the “anti security” movement, or #AntiSec, a group made up by “Anonymous” and “LulzSec” have released details that could put us all in danger if they do as LulzSec did after their 50 day rampage across the internet, they released the files they obtained.
It seems as though AntiSec claims to have passwords to Apple’s servers and a bunch of administrative usernames as well. Not just that, they have said that they managed to hack iCloud as well.
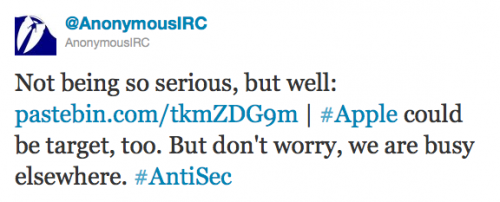
Here is what LulzSec had to say:
Some weeks ago, we smashed into the iCloud with our heavy artillery Lulz Cannons and decided to switch to ninja mode. From our LFI entry point, we acquired command execution via local file inclusion of enemy fleet Apache vessel. We then found that the HTTPD had SSH auth keys, which let our ship SSH into other servers. See where this is going?
We then switched to root ammunition rounds. And we rooted… and rooted… and rooted… After mapping their internal network and thoroughly pillaging all of their servers, we grabbed all their source code and database passwords, which we proceeded to shift silently back to our storage deck.
Again, at the moment Apple has not implemented all of iCloud’s security features, as this is a developer only preview, but still, we can only hope that this will force Apple to beef up security on their servers.
Incoming search terms:
- icloud hack
- icloud hacks
- hack icloud
- icloud hacked
- can icloud be hacked
- ANTISEC torrent
- icloud hacking
One more thing. I think that there are quite a few travel insurance sites of dependable companies that let you enter your journey details and obtain you the quotations. You can also purchase an international holiday insurance policy on-line by using your current credit card. All you need to do is usually to enter all travel particulars and you can view the plans side-by-side. Only find the program that suits your financial allowance and needs after which use your bank credit card to buy them. Travel insurance online is a good way to search for a reliable company with regard to international holiday insurance. Thanks for discussing your ideas.